Stolen NSA spy weapon used in global ‘ransomware’ attacks
yber criminals have exploited spy tools stolen from the US National Security Agency (NSA) to launch a massive “ransomware” attack in nearly 100 countries around the world, security researchers say.
In mid-April, an arsenal of powerful hacking tools apparently designed by the NSA was leaked by an entity known only as the “Shadow Brokers,” sparking concerns that hackers might use the cyber weapons against the general public.
That has become reality nearly a month later as tens of thousands of computers around the world have become crippled by an unknown hacking group demanding ransom.
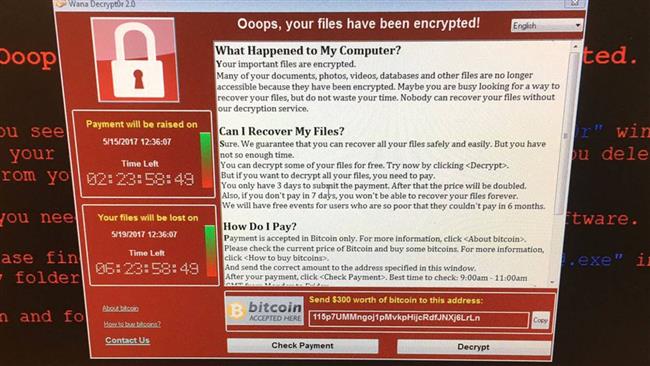
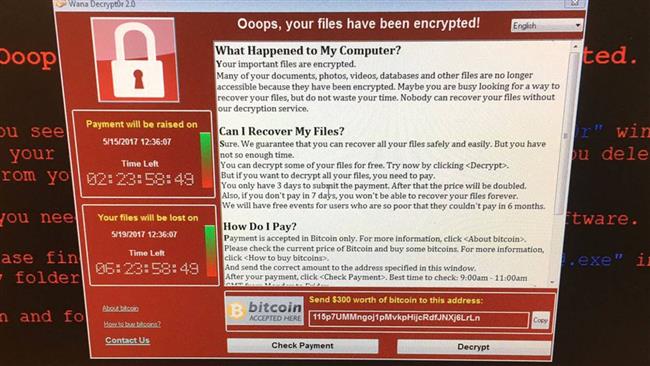
The malicious malware called “WannaCry” locks down all the files on an infected computer and asks the administrator to pay $300 to $600 in order to restore access.
Researchers with security software maker Avast said they had tracked 75,000 cases of ransomware infections in 99 countries, with Russia, Ukraine and Taiwan being the top targets.
Russia’s Interior Ministry released a statement confirming a ransomware attack on its computers. The statement said the virus was now “localized” and antivirus systems were working to destroy it.
In Britain, National Health Service (NHS) hospitals and clinics were forced to turn away patients after losing access to computers.
Spanish telecom company Telefónica was also hit with the ransomware.
“This is one of the largest global ransomware attacks the cyber community has ever seen,” said Rich Barger, director of threat research with Splunk, one of the firms that linked ransomware to the NSA.

The software weapon would have allowed NSA hackers to break into millions of Windows computers by taking advantage of a flaw in a network protocol of the operating system.
Microsoft fixed the vulnerability in a March software update. But computers and networks that have not kept their systems current with the most recent updates are at risk.
The US Department of Homeland Security released a statement on Friday urging people to update their operating systems.
“We are actively sharing information related to this event and stand ready to lend technical support and assistance as needed to our partners, both in the United States and internationally,” the department said.
A small number of US-headquartered organizations were also hit on Friday.